2020. 12. 19. 02:37ㆍ카테고리 없음
In cryptography, a transposition cipher is a method of encryption by which the positions held by units of plaintext (which are commonly characters or groups of characters) are shifted according to a regular system, so that the ciphertext constitutes a permutation of the plaintext. That is, the order of the units is changed (the plaintext is reordered). Mathematically a bijective function is used on the characters' positions to encrypt and an inverse function to decrypt.
Police crack modus operandi of cyber gang R. Sivaraman CHENNAI, November 16, 2020 04:13 IST Updated: November 16, 2020 04:13 IST R. Sivaraman CHENNAI, November 16, 2020 04:13 IST. How To Decrypt The Floppy Disk. Players take on the role of “Bell” in Call Of Duty: Black Ops Cold War (at least when they’re not playing as Mason).Bell is the one who will do the actual. Liquid e-juice offers the best affordable vape juice & e-liquid products with high-quality vapor flavors bringing the best American E-juice’s to Canada. Council pounces on illegal operations. By newsday.co.zw - December 7, 2020. Police threaten to crack down on ‘cyber-bullying’ on Mnangagwa officials newsday.co.zw December 8, 2020.
Following are some implementations.
Rail Fence cipher[edit]
The Rail Fence cipher is a form of transposition cipher that gets its name from the way in which it is encoded. In the rail fence cipher, the plaintext is written downwards and diagonally on successive 'rails' of an imaginary fence, then moving up when we get to the bottom. The message is then read off in rows. For example, using three 'rails' and a message of 'WE ARE DISCOVERED FLEE AT ONCE', the cipherer writes out:
Then reads off: Angelbird wrk for mac.
(The cipher has broken this ciphertext up into blocks of five to help avoid errors. This is a common technique used to make the cipher more easily readable. The spacing is not related to spaces in the plaintext and so does not carry any information about the plaintext.)
Scytale[edit]
The rail fence cipher follows a pattern similar to that of the scytale, a mechanical system of producing a transposition cipher used by the ancient Greeks. The system consisted of a cylinder and a ribbon that was wrapped around the cylinder. The message to be encrypted was written on the coiled ribbon. The letters of the original message would be rearranged when the ribbon was uncoiled from the cylinder. However, the message was easily decrypted when the ribbon was recoiled on a cylinder of the same diameter as the encrypting cylinder.[1]. Using the same example as before, if the cylinder has a radius such that only three letters can fit around its circumference, the cipherer writes out:
In this example, the cylinder is running horizontally and the ribbon is wrapped around vertically. Hence, the cipherer then reads off:
Route cipher[edit]
In a route cipher, the plaintext is first written out in a grid of given dimensions, then read off in a pattern given in the key. For example, using the same plaintext that we used for rail fence:
The key might specify 'spiral inwards, clockwise, starting from the top right'. That would give a cipher text of:
Route ciphers have many more keys than a rail fence. In fact, for messages of reasonable length, the number of possible keys is potentially too great to be enumerated even by modern machinery. However, not all keys are equally good. Badly chosen routes will leave excessive chunks of plaintext, or text simply reversed, and this will give cryptanalysts a clue as to the routes. Divx converter mac free download.
A variation of the route cipher was the Union Route Cipher, used by Union forces during the American Civil War. This worked much like an ordinary route cipher, but transposed whole words instead of individual letters. Because this would leave certain highly sensitive words exposed, such words would first be concealed by code. The cipher clerk may also add entire null words, which were often chosen to make the ciphertext humorous.[citation needed]
Columnar transposition[edit]
In a columnar transposition, the message is written out in rows of a fixed length, and then read out again column by column, and the columns are chosen in some scrambled order. Both the width of the rows and the permutation of the columns are usually defined by a keyword. For example, the keyword ZEBRAS is of length 6 (so the rows are of length 6), and the permutation is defined by the alphabetical order of the letters in the keyword. In this case, the order would be '6 3 2 4 1 5'.
In a regular columnar transposition cipher, any spare spaces are filled with nulls; in an irregular columnar transposition cipher, the spaces are left blank. Finally, the message is read off in columns, in the order specified by the keyword. For example, suppose we use the keyword ZEBRAS and the message WE ARE DISCOVERED. FLEE AT ONCE. In a regular columnar transposition, we write this into the grid as follows:
providing five nulls (QKJEU), these letters can be randomly selected as they just fill out the incomplete columns and are not part of the message. The ciphertext is then read off as:
In the irregular case, the columns are not completed by nulls:
This results in the following ciphertext:
To decipher it, the recipient has to work out the column lengths by dividing the message length by the key length. Then he can write the message out in columns again, then re-order the columns by reforming the key word.
In a variation, the message is blocked into segments that are the key length long and to each segment the same permutation (given by the key) is applied. This is equivalent to a columnar transposition where the read-out is by rows instead of columns.
Columnar transposition continued to be used for serious purposes as a component of more complex ciphers at least into the 1950s.
Double transposition[edit]
A single columnar transposition could be attacked by guessing possible column lengths, writing the message out in its columns (but in the wrong order, as the key is not yet known), and then looking for possible anagrams. Thus to make it stronger, a double transposition was often used. This is simply a columnar transposition applied twice. The same key can be used for both transpositions, or two different keys can be used.
As an example, we can take the result of the irregular columnar transposition in the previous section, and perform a second encryption with a different keyword, STRIPE, which gives the permutation '564231':
As before, this is read off columnwise to give the ciphertext:
If multiple messages of exactly the same length are encrypted using the same keys, they can be anagrammed simultaneously. This can lead to both recovery of the messages, and to recovery of the keys (so that every other message sent with those keys can be read).
During World War I, the German military used a double columnar transposition cipher, changing the keys infrequently. The system was regularly solved by the French, naming it Übchi, who were typically able to quickly find the keys once they'd intercepted a number of messages of the same length, which generally took only a few days. However, the French success became widely known and, after a publication in Le Matin, the Germans changed to a new system on 18 November 1914.[2]
During World War II, the double transposition cipher was used by Dutch Resistance groups, the French Maquis and the British Special Operations Executive (SOE), which was in charge of managing underground activities in Europe.[3] It was also used by agents of the American Office of Strategic Services[4] and as an emergency cipher for the German Army and Navy.
Visual studio code download mac. Until the invention of the VIC cipher, double transposition was generally regarded as the most complicated cipher that an agent could operate reliably under difficult field conditions.
Cryptanalysis[edit]
The double transposition cipher can be treated as a single transposition with a key as long as the product of the lengths of the two keys.[5] https://ys3.weebly.com/lisp-for-mac.html.
In late 2013, a double transposition challenge, regarded by its author as undecipherable, was solved by George Lasry using a divide-and-conquer approach where each transposition was attacked individually.[6]
Myszkowski transposition[edit]

A variant form of columnar transposition, proposed by Émile Victor Théodore Myszkowski in 1902, requires a keyword with recurrent letters. In usual practice, subsequent occurrences of a keyword letter are treated as if the next letter in alphabetical order, e.g., the keyword TOMATO yields a numeric keystring of '532164.'
In Myszkowski transposition, recurrent keyword letters are numbered identically, TOMATO yielding a keystring of '432143.'
Plaintext columns with unique numbers are transcribed downward;those with recurring numbers are transcribed left to right:
Disrupted transposition[edit]
The disrupted transposition cipher is a further complication to the normal transposition technique. Instead of filling the matrix row by row, the rows are all filled in irregular fashion. This results in a very complex transposition of the characters. First, we determine the exact number of rows and columns to fill. Next, we fill a row until we reach the first alphabet sequence from the keyword sequence. If the first digit is at the 8th place, we will only fill that row up to that position. We continue the next row until the second position and so on based on the given example. If we have reached the end position of the last line we continue by filling the remaining empty places at each line. In our example the difference between the two areas is visible by the lower and upper case
characters.
The plain text:
“We confirm the delivery of the documents later”
We use the key BIRTHDAY
On the matrix1: after filling the first area
On the matrix2: we see the same matrix
filled completely:
Matrix1:
| 2 | 5 | 6 | 7 | 4 | 3 | 1 | 8 |
|---|---|---|---|---|---|---|---|
| B | I | R | T | H | D | A | Y |
| W | E | C | O | N | F | I | |
| R | |||||||
| M | T | H | E | D | E | ||
| L | I | V | E | R | |||
| Y | O | ||||||
| F | T | H | |||||
| E | D | O | C | ||||
| U | M | E | N | T | S | L | A |
Matrix2:
| 2 | 5 | 6 | 7 | 4 | 3 | 1 | 8 |
|---|---|---|---|---|---|---|---|
| B | I | R | T | H | D | A | Y |
| W | E | C | O | N | F | I | t |
| R | e | r | |||||
| M | T | H | E | D | E | ||
| L | I | V | E | R | |||
| Y | O | ||||||
| F | T | H | |||||
| E | D | O | C | ||||
| U | M | E | N | T | S | L | A |
Once the matrix is filled we read it off by the columns, Best torrent engine.
according to the keyword sequence.
The Cipher Text:
https://resttrammare1987.mystrikingly.com/blog/skate-2-for-mac. ILWRMLYFEUFESNDRTEETIOTDMCRHVHOEOEECNTA
Grilles[edit]
Another form of transposition cipher uses grilles, or physical masks with cut-outs. This can produce a highly irregular transposition over the period specified by the size of the grille, but requires the correspondents to keep a physical key secret. Grilles were first proposed in 1550, and were still in military use for the first few months of World War One.
Detection and cryptanalysis[edit]
Since transposition does not affect the frequency of individual symbols, simple transposition can be easily detected by the cryptanalyst by doing a frequency count. If the ciphertext exhibits a frequency distribution very similar to plaintext, it is most likely a transposition. This can then often be attacked by anagramming—sliding pieces of ciphertext around, then looking for sections that look like anagrams of English words, and solving the anagrams. Once such anagrams have been found, they reveal information about the transposition pattern, and can consequently be extended.
Simpler transpositions also often suffer from the property that keys very close to the correct key will reveal long sections of legible plaintext interspersed by gibberish. Consequently, such ciphers may be vulnerable to optimum seeking algorithms such as genetic algorithms.[7]
A detailed description of the cryptanalysis of a German transposition ciphercan be found in chapter 7 of Herbert Yardley's 'The American Black Chamber.'
A cipher used by the Zodiac Killer, called 'Z-340', organized into triangular sections with substitution of 63 different symbols for the letters and diagonal 'knight move' transposition, remained unsolved for over 51 years, until an international team of private citizens cracked it on December 5, 2020 using specialized software.[8]
Combinations[edit]
Transposition is often combined with other techniques such as evaluation methods. For example, a simple substitution cipher combined with a columnar transposition avoids the weakness of both. Replacing high frequency ciphertext symbols with high frequency plaintext letters does not reveal chunks of plaintext because of the transposition. Anagramming the transposition does not work because of the substitution. The technique is particularly powerful if combined with fractionation (see below). A disadvantage is that such ciphers are considerably more laborious and error prone than simpler ciphers.
Fractionation[edit]
Transposition is particularly effective when employed with fractionation – that is, a preliminary stage that divides each plaintext symbol into several ciphertext symbols. For example, the plaintext alphabet could be written out in a grid, and every letter in the message replaced by its co-ordinates (see Polybius square and Straddling checkerboard).[9]Another method of fractionation is to simply convert the message to Morse code, with a symbol for spaces as well as dots and dashes.[10]
When such a fractionated message is transposed, the components of individual letters become widely separated in the message, thus achieving Claude E. Shannon's diffusion. Examples of ciphers that combine fractionation and transposition include the bifid cipher, the trifid cipher, the ADFGVX cipher and the VIC cipher.
Another choice would be to replace each letter with its binary representation, transpose that, and then convert the new binary string into the corresponding ASCII characters. Looping the scrambling process on the binary string multiple times before changing it into ASCII characters would likely make it harder to break. Many modern block ciphers use more complex forms of transposition related to this simple idea.
See also[edit]
Notes[edit]
- ^Smith, Laurence Dwight (1955) [1943], Cryptography / The Science of Secret Writing, New York: Dover, pp. 16, 92–93
- ^Kahn, pp. 301-304.
- ^Kahn, pp. 535 and 539.
- ^Kahn, p. 539.
- ^Barker, Wayne (1995). Cryptanalysis of the Double Transposition Cipher: Includes Problems and Computer Programs. Aegean Park Press.
- ^Lasry, George (2014-06-13). 'Solving the Double Transposition Challenge with a Divide-and-Conquer Approach'. Cryptologia. 38 (3): 197–214. doi:10.1080/01611194.2014.915269. S2CID7946904.
- ^doi:10.1080/0161-119391867863 Robert A. J. Matthews pages 187-201
- ^'Zodiac Killer cipher is cracked after eluding sleuths for 51 years'. arstechnica.com. 2020-12-12. Retrieved 2020-12-12.
- ^Daniel Rodriguez-Clark.'Transposing Fractionated Ciphertext'.
- ^James Lyons.'Fractionated Morse Cipher'.
Cyber Ops Crack Games
References[edit]
- Kahn, David. The Codebreakers: The Story of Secret Writing. Rev Sub. Scribner, 1996.
- Yardley, Herbert. The American Black Chamber. Bobbs-Merrill, 1931.
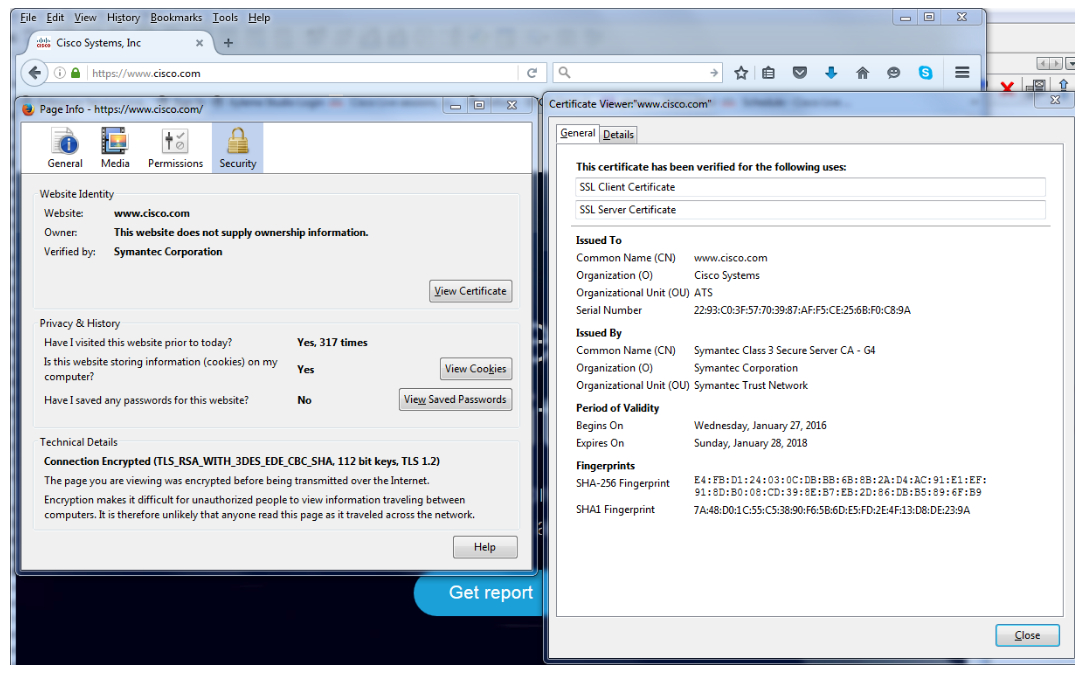
Equip you to solve all exam questions
Now think of any Cisco certification exam, Crack4sure provides you the pathway to success with 100% Money Back Guarantee! The cutting-edge content of Crack4sure’s study guides, dumps, practice questions and answers best equips you with the required information and hands-on practice to ace exam for the very time you take it.
Perfection and Precision
Crack4sure makes its mark by providing you the best Cisco CyberOps Associate questions and answers, richly packed with the best possible information on your exam syllabus. The information has been drawn from all the recommended sources provided by the vendors. Ps3 eye drivers for mac. To further enhance the content, our experts have utilized the most authentic and verified sources and thus prepared the Cisco CyberOps Associate study questions in our dumps and study guides most suitable and relevant for the exam candidates.
Easy and Reliable Cisco CyberOps Associate Questions and Answers
The Cisco CyberOps Associate questions and answers in our study guides and dumps have been made consciously easy and graspable so that all exam takers learn them without any hassle and in minimum time. As a result, they never pose any hurdle in your learning as it often happens in case of un-authentic online course free or any other substandard source of learn online. Our Cisco CyberOps Associate products prove immensely beneficial to all exam takers because they have been crafted keeping in view the actual needs of test takers and provide them maximum benefit.
Try also our Cisco CyberOps Associate testing engine facility to get practice questions and answers that introduce you to the actual exam format and the study questions, you are expected to answer in the real exam.
Cyber Ops Crack Download
Cisco CyberOps Associate Passing Assurance
The most remarkable feature of our Cisco CyberOps Associate products is that they provide each client exam passing guarantee with the promise of paying back the money they spent in buying our product. There is no chance of failing the exam, if you prepare for exam using our Cisco CyberOps Associate study guides and Cisco CyberOps Associate dumps. You are assured with an outstanding exam success in the very first attempt.
Cyber Ops Crack Torrent
Free Cisco CyberOps Associate Product Demo
Cyber Ops Crack Pc
Before you actually buy any product from us, download its free demo and compare the quality of Cisco CyberOps Associate questions and answers with VCE files and with the products of our competitors such as exam collection and so on. We firmly believe that you will find our products far more superior than any other study material.